Your GRC Portfolio Is Outdated (Here’s What Hiring Managers Want in 2026)
If Your GRC Projects Look Like Paperwork, You’re Doing It Wrong
In my 20+ career in Cybersecurity .. I must have reviewed over thousands of Governance, Risk and Compliance (GRC) resumes
A recurring mistake I see people make when trying to break into GRC is confusing activity with impact.
They map controls to frameworks, write policies no one will read, and proudly list every standard they’ve “worked with.” ISO 27001. NIST. SOC 2. PCI DSS. EU AI Act.
On paper, it looks impressive. In reality, it tells me very little.
If you want your GRC profile to stand out in 2026, you need to stop treating governance, risk, and compliance as documentation work and start treating it as decision-making under real constraints.
What hiring managers and security leaders actually want to see is whether you understand why controls exist, when they matter, when they don’t, and how to justify security decisions when the answer isn’t obvious.
Real GRC work is messy. Requirements are vague. Business constraints are real. Perfect compliance is almost never achievable. And most of the job involves explaining uncomfortable truths to people who would rather hear simple answers.
Strong GRC projects reflect this reality. Weak ones look like coursework.
If your GRC projects are just screenshots, control mappings, or copied policy templates, they’re not helping you. Everyone can do that now. AI can do that. What differentiates strong GRC professionals is judgment.
Below are five GRC projects that consistently signal maturity, not because they are complex, but because they mirror how governance and risk decisions are actually made inside organisations.
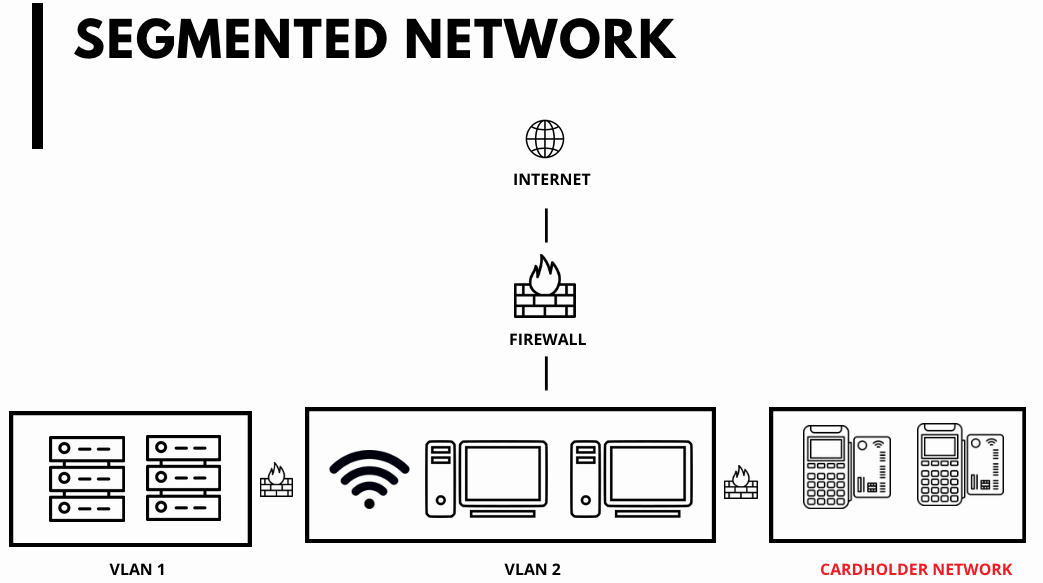
1 — Reviewing Network Segmentation for PCI DSS
PCI DSS is one of the fastest ways to expose whether someone understands real-world GRC or just compliance theatre.
Most people approach PCI segmentation as a diagram exercise. Draw a cardholder data environment, draw a line around it, label it “segmented,” and move on. That might pass a slide review, but it won’t survive a serious audit or a breach.
A strong GRC project treats segmentation as a risk claim that must be defended.
You start by defining what actually constitutes the CDE, not what people wish it were. You examine trust relationships, shared services, jump hosts, logging paths, and administrative access. You ask uncomfortable questions about implicit trust and lateral movement.
Then you do the part that really matters. You assess whether segmentation genuinely reduces scope or merely creates a false sense of safety. You document where the design holds and where it doesn’t. You explain what a QSA would likely challenge and why.
This kind of project demonstrates that you understand compliance is not about diagrams. It’s about whether your argument would still stand when things go wrong.
2 — Justifying a Statement of Applicability in ISO 27001
The Statement of Applicability is one of the most misunderstood artifacts in ISO 27001.
Junior practitioners often treat it like a checklist. Include everything to be safe. Mark controls as “implemented” even when they’re aspirational. Avoid exclusions because exclusions feel risky.
Experienced GRC professionals know the opposite is true. Over-including controls creates audit debt. It creates obligations the organisation cannot realistically sustain. And it weakens credibility with auditors who can spot box-ticking instantly.
A strong GRC project builds a risk-driven SoA that explicitly excludes controls and defends those exclusions.
You tie each exclusion back to the risk assessment. You explain why a control is not applicable in the organisation’s context. You document alternative measures where appropriate. And you anticipate auditor pushback by explaining what evidence you would present and where you would reconsider the decision.
This shows that you understand ISO 27001 is not about maximal compliance. It’s about proportionate, defensible security aligned to business reality.
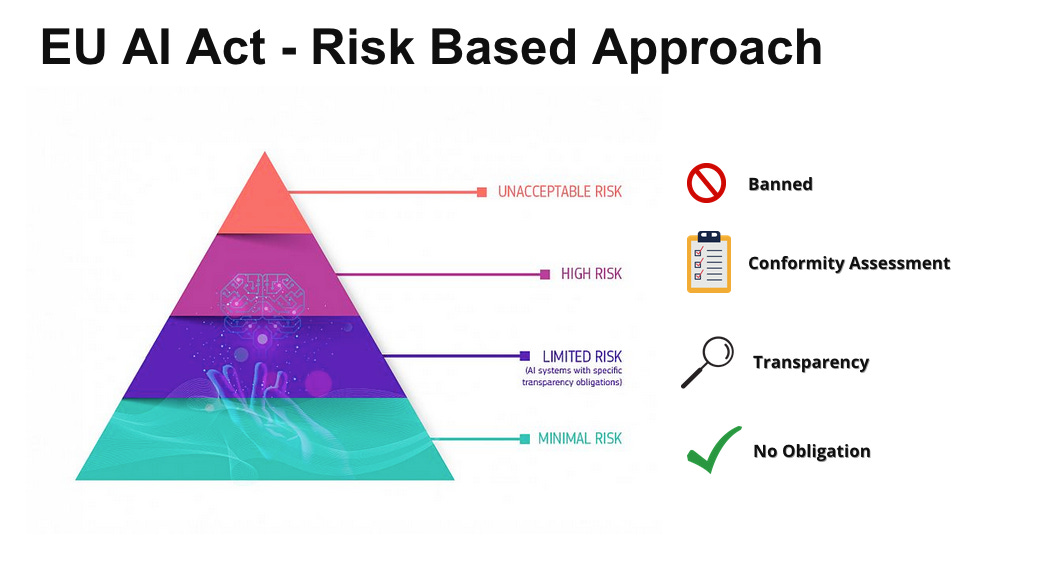
3 — Assessing a High-Risk AI Use Case Under the EU AI Act
The EU AI Act has created a flood of shallow content. Summaries of articles. Lists of obligations. High-risk classifications with no operational depth.
A meaningful GRC project goes much further.
You take a realistic AI use case, such as candidate screening, credit decisioning, or biometric identification, and treat it as if it were about to be reviewed by a regulator.
You define the system’s purpose clearly. You document decision boundaries. You examine data sources, training assumptions, and feedback loops. You assess whether human oversight is meaningful or merely symbolic. You identify risks to fundamental rights, not just technical failure modes.
Then you do the hard part. You decide whether the system should be deployed at all.
This project demonstrates that you can translate regulation into operational reality. It shows you understand that AI governance is not about compliance checklists. It’s about preventing harm before it happens.
4 — Automating a GRC Control
One of the biggest shifts happening quietly in GRC is the move toward what many now call GRC engineering.
Traditional GRC relies heavily on manual processes. Quarterly reviews. Spreadsheet evidence. Screenshots attached to tickets. Email confirmations. These controls technically exist, but they fail silently and frequently.
A strong project takes a common control, such as privileged access review or configuration compliance, and redesigns it to be automated and continuous.
You start by identifying the control intent. Then you map the manual steps and their failure points. Finally, you design a system that produces evidence automatically, detects drift, and alerts when thresholds are breached.
What makes this project powerful is not the tooling. It’s the explanation. You show what has been automated, what remains manual, what evidence auditors will see, and what residual risk still exists.
This signals that you understand both governance requirements and engineering reality. That combination is becoming increasingly rare and increasingly valuable.
Watch my below video for more details
5 — Writing a Risk Acceptance for a Security Gap (without drowning in technical jargon)
Every organisation has risks it chooses to live with. The difference between strong and weak GRC is whether those decisions are intentional and defensible.
Many risk acceptances fail not because the risk is unreasonable, but because the explanation is.
A common mistake is drowning decision-makers in technical jargon. Instead of explaining the risk in plain terms, the document becomes a mini penetration test report. Terms like credential stuffing, lateral movement, attack surface, and privilege escalation are used without context. Executives are left confused, not informed.
Another frequent failure is hiding behind vague language. Phrases like “risk is low,” “controls are in place,” or “mitigated appropriately” appear without evidence or explanation. This may feel safer, but it actually weakens accountability.
Some documents try to sell the decision instead of explaining it. They downplay impact, inflate control effectiveness, or avoid mentioning trade-offs. Experienced leaders recognise this immediately and lose trust in the process.
Finally, many candidates forget that risk acceptance is a business decision, not a security permission slip. The goal is not to eliminate risk, and it’s not to scare leadership into remediation. The goal is to present a clear, honest picture so the business can choose knowingly.
A strong risk acceptance does exactly that. It is readable, specific, defensible, and uncomfortable in the right way. It shows that GRC exists to enable informed risk-taking, not to bury decisions under technical noise.
Packaging GRC Work Like a Professional
Just like cloud security projects, GRC projects should be presented as case studies, not artifacts.
A strong portfolio lives in a clean GitHub repository or structured workspace. Each project explains the scenario, assumptions, constraints, decisions, and trade-offs. Diagrams are used where they clarify thinking, not to decorate.
The real differentiator is walking someone through your reasoning. A short Loom video where you explain why you made certain decisions is far more powerful than any checklist or certificate.
It shows how you think. It shows how you communicate risk. And it shows whether you can operate in the grey areas where real GRC work lives.
Why This Approach Works
The GRC market has matured. Framework familiarity is assumed. Documentation alone is no longer impressive. What organisations need are people who can interpret requirements, balance competing priorities, and defend decisions when challenged.
Projects like these work because they reflect reality. They show judgment, not memorisation. They show governance as a living system, not a static set of documents.
If you do one or two GRC projects at this depth, they will outweigh a long list of frameworks on your CV. You are not proving that you can follow rules. You are proving that you can help an organisation make better security decisions.
That is what makes a GRC professional stand out in 2026
If you still need help check out my video below which also has a full repo with these projects


Where can I find your repo?