The Ultimate Guide to Starting a Cybersecurity GRC Career in 2026
How to Break Into GRC Even Without Technical Experience
If you’ve been following the cybersecurity world over the past year, you’ll notice a strange paradox.
AI is automating huge parts of security operations. SOC work is changing. Pentesting is shifting. Cloud engineering is becoming AI-assisted. And many people feel more uncertain about their cybersecurity careers than ever before.
Yet at the same time, organizations are facing a tidal wave of new regulations, AI governance obligations, supply-chain risks, identity challenges, and digital-resilience requirements.
And in the middle of all that…
GRC has quietly become one of the fastest-growing, most stable, and most accessible career paths in cybersecurity.
Not because it’s simple. Not because it avoids technical concepts.
But because modern GRC sits at the intersection of cybersecurity, business strategy, AI governance, cloud architecture, regulatory pressure, and operational resilience.
Over the past few years, I’ve helped hundreds of people transition into GRC — accountants, HR professionals, admins, engineers, teachers, nurses, project managers. Many felt cybersecurity was “too technical” until they discovered GRC.
Because GRC isn’t about writing code or configuring firewalls.
It’s about understanding risk, communicating clearly, thinking analytically, and translating complex ideas into business impact.
This guide will show you exactly how to break into GRC in 2026 — even if you have no technical background — and how to build the kind of portfolio that gets recruiters saying:
“We want to talk to you.”
Let’s begin.
What GRC Actually Is — And Why It Matters More Than Ever in 2026
GRC (Governance, Risk & Compliance) professionals help organizations:
identify and analyze risks
build and monitor controls
comply with global regulations
govern AI systems and models
manage cloud, identity, and third-party risk
align cybersecurity with business strategy
build digital resilience, not just security
In 2026, this has expanded dramatically.
New regulations and standards like the EU AI Act, ISO 4001, NIST AI Risk Management Framework are reshaping expectations for organizations across every industry — from retail to fintech to healthcare to SaaS.
Add to that:
AI systems performing autonomous actions
machine identities outnumbering human identities
supply-chain breaches dominating headlines
the rise of continuous monitoring
cloud-native systems evolving daily
…and it becomes clear why GRC professionals are more in demand than ever before.
In fact, GRC has become the career path where communication and business understanding are often more important than deep technical expertise.
The Biggest Mistake People Make When Entering GRC
Many newcomers try to enter GRC by:
learning hacking
doing SOC analyst courses
focusing on technical certs
memorizing definitions
copying generic templates
None of that helps.
Because GRC isn’t about technical execution.
It’s about governance, judgment, prioritization, clarity, structure, and risk-based thinking.
The right approach is different — and far more strategic.
How to Break Into GRC in 2026 (A Clear, Practical Roadmap)
1 — Master the Frameworks & Regulations That Actually Matter
In 2026, employers expect you to understand the major frameworks shaping global cybersecurity governance — not at expert level, but at a functional, conversational level.
Start with the foundations:
ISO 27001:2022 — the global standard for information security
SOC 2 — trust criteria for service based organization
PCI DSS 4.0 — mandatory for payment security
GDPR — still the backbone of privacy regulation
Then add the 2025–2026 transformers:
EU AI Act — AI risk classification + governance obligations
NIST CSF 2.0 — updated cyber governance framework
NIST AI RMF — AI risk management principles
When you understand these, you understand the language of modern GRC — a language that combines cyber controls, AI risk, resilience, supply chain, and identity governance.
2 — Learn Through Case Studies (Not Textbooks or Theory)
Textbook knowledge rarely helps you in GRC interviews. What matters is whether you can demonstrate practical, scenario-based thinking.
Instead of reading definitions, study real-world examples:
How a retailer implemented PCI DSS 4.0 and dealt with multi-factor authentication failures.
How a bank aligned their ICT asset register and incident classification process with DORA.
How a SaaS startup applied the EU AI Act to classify their model as “high-risk” and redesign their governance workflow.
How an e-commerce company mapped ISO 27001 Annex A controls to actual cloud services.
How supply-chain failures led to several major 2025 breaches — and what governance gaps caused them
These case studies give you interview stories, portfolio ideas, and practical confidence. They also train your brain to think like a GRC professional: holistically, contextually, and with a business-first mindset.
3 — Choose Certifications That Actually Matter for GRC
Certifications can be helpful — but only the right ones.
If you’re just starting, ISC² Certified in Cybersecurity (CC) or CompTIA Security+ give you a foundation in terminology and basic concepts.
Once you understand the basics, move toward certifications that directly enhance GRC skills, such as ISO 27001 Lead Implementer or CRISC
As AI governance becomes mainstream, new certifications in responsible AI, AI assurance, and AI risk management are emerging — these will differentiate you over the next few years.
At the senior level, CISM and CISSP remain gold standards, especially if you lean toward governance-heavy domains.
Just remember:
Certifications open the door.
Practical skills get you hired.
4 — Develop Communication Skills
This is where a lot of professionals goof up. They never work on improving their communication skills.
GRC is a communication-heavy discipline.
You are constantly translating complex issues into business impact.
You will need to explain risk to executives who don’t understand technology, and technology to developers who don’t understand risk. You’ll write reports, present findings, shape policies, persuade stakeholders, and sometimes push back on decisions that increase risk.
Clarity, structure, and the ability to deliver uncomfortable truths diplomatically are core GRC skills. In 2026, the professionals who rise the fastest aren’t the most technical — they are the ones who can influence, communicate, and simplify.
5 — Build Practical Experience (Even Without a Job Offer)
The biggest misconception about GRC is that you need a job before you can gain experience. The opposite is true.
GRC experience is something you create — not something you wait for.
Start by helping small organizations that need cybersecurity support:
nonprofits
early-stage startups
small retail shops
local service businesses
community groups
Offer to run a basic risk assessment, perform an ISO 27001 gap review, assess their access controls, classify any AI tools they use, or build simple policies. Many will say yes — because they genuinely need the help.
Alongside this, build your own practice projects:
create a risk register
map ISO controls to cloud services
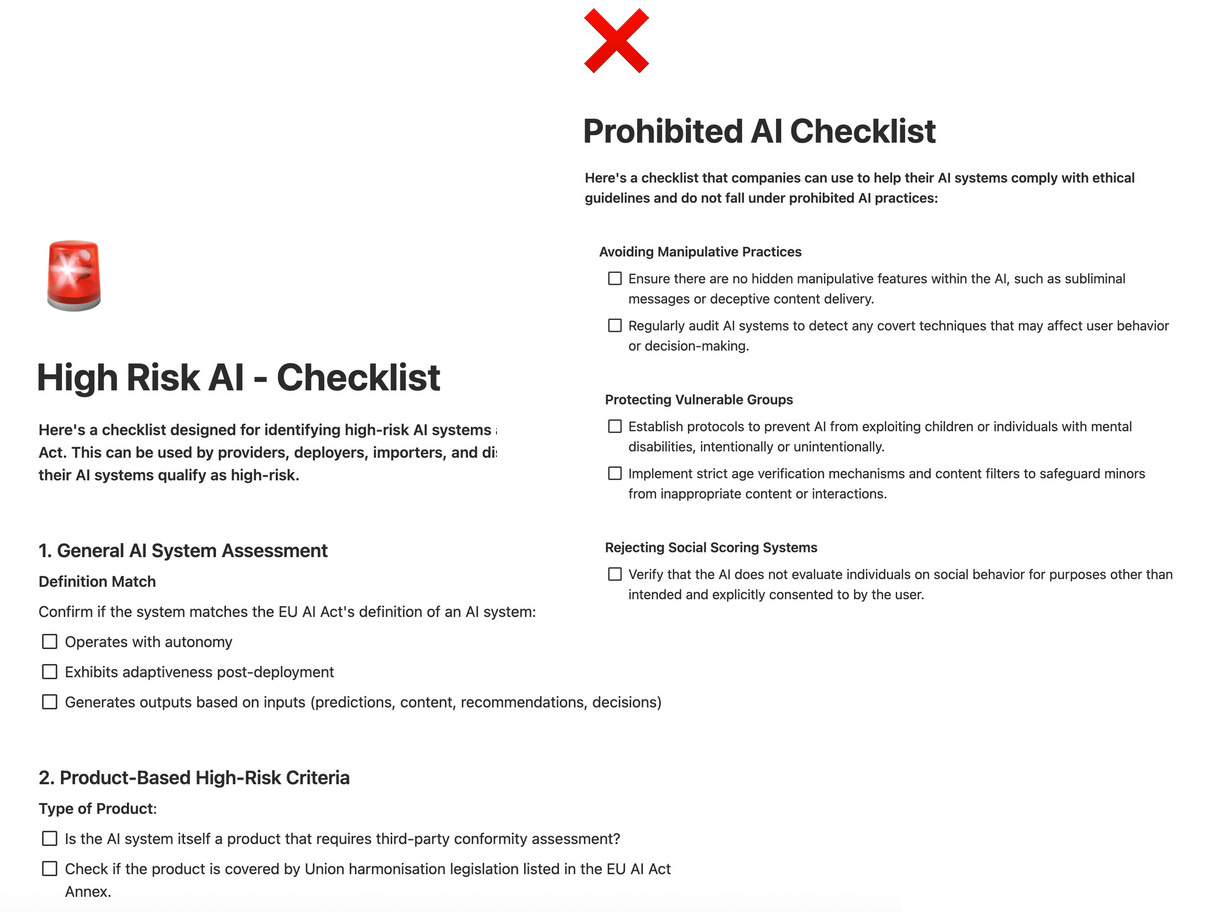
build an audit checklist
draft a security policy pack
design a cloud governance model
complete an AI governance assessment
These become your portfolio — concrete evidence of your skills.
And here’s a powerful 2026 strategy few people use:
Create a simple GRC checklist in Notion, such as:
“20 Essential Steps for ISO 27001 Readiness”
“A Beginner’s AI Governance Checklist for Startups”
“DORA Readiness: The Five Controls You Can Start Today”
Make it clean, visual, and structured.
Then publish it on LinkedIn as a free resource.
This does three things instantly:
It demonstrates your understanding of frameworks and controls.
It positions you as a contributor to the GRC community rather than a passive learner.
It gives employers evidence of how you think, structure, and communicate.
People routinely underestimate how much this matters. When you publish a practical Notion checklist, a mini risk assessment template, or a small GRC resource, the conversation with recruiters shifts immediately from:
“Do you have experience?” to “I saw your checklist — can we talk about how you approached it?”
That is how people break into GRC in 2026 — by showing their work before anyone asks for it.
6 — Understand the New Trends Transforming GRC in 2026
The GRC landscape is shifting dramatically — and newcomers who understand these trends stand out immediately.
AI Governance & Model Risk
The EU AI Act and NIST AI RMF are pushing companies to classify and govern AI systems. Shadow AI is causing breaches. Machine identities are exploding. Identity governance is becoming more complex than ever.
GRC Engineering
The biggest transformation in GRC.
Organizations now want professionals who can think like engineers:
automate evidence
integrate controls with cloud logs
build continuous assurance
create policy-as-code workflows
design scalable governance patterns
If old GRC was spreadsheets and checklists…
modern GRC is engineering.
Final Thoughts
If you’ve ever felt cybersecurity was “too technical,” this is your moment.
2026 has made GRC:
more important
more strategic
more business-focused
more stable
more accessible
and more future-proof than ever before
You don’t need to code. You don’t need to hack. You don’t need to be deep technical.
You need four things:
the frameworks
the communication skills
the portfolio
the mindset
Follow the roadmap above, create visible public proof of your skills, embrace the new GRC trends, and you will be ahead of 99% of people trying to enter cybersecurity right now.
A Quick Word If You Want to Go Beyond Theory…
If you want to learn GRC the way organizations actually practice it in 2026 —
continuous monitoring, automation, policy-as-code, AI governance, cloud risk, IAM governance, real case studies, and GRC Engineering workflows — my GRC Engineering Masterclass might help.
It’s for people who want to move from knowing GRC to doing GRC.
Just mentioning it in case you want to take the next step !


I truly appreciate the read, I am currently working towards my degree and wasn't sure of the proper direction to take for GRC so this helps me get a good heading for where to begin and love the straight forward approach of the article and how it is not about copying templates but actually understanding the frameworks more than the memorization of the definitions.
Great read