The Right and the Wrong Way to Learn AWS Security in 2026
Why memorizing AWS services won’t make you secure in 2026
AWS security is still hot in 2026. Cloud adoption hasn’t slowed down. If anything, it has deepened. Startups are born directly into multi-account AWS environments. Enterprises are migrating critical systems, not just experiments. Regulators are increasing scrutiny. Boards are asking sharper questions. And in every one of those scenarios, cloud security is not optional — it’s foundational.
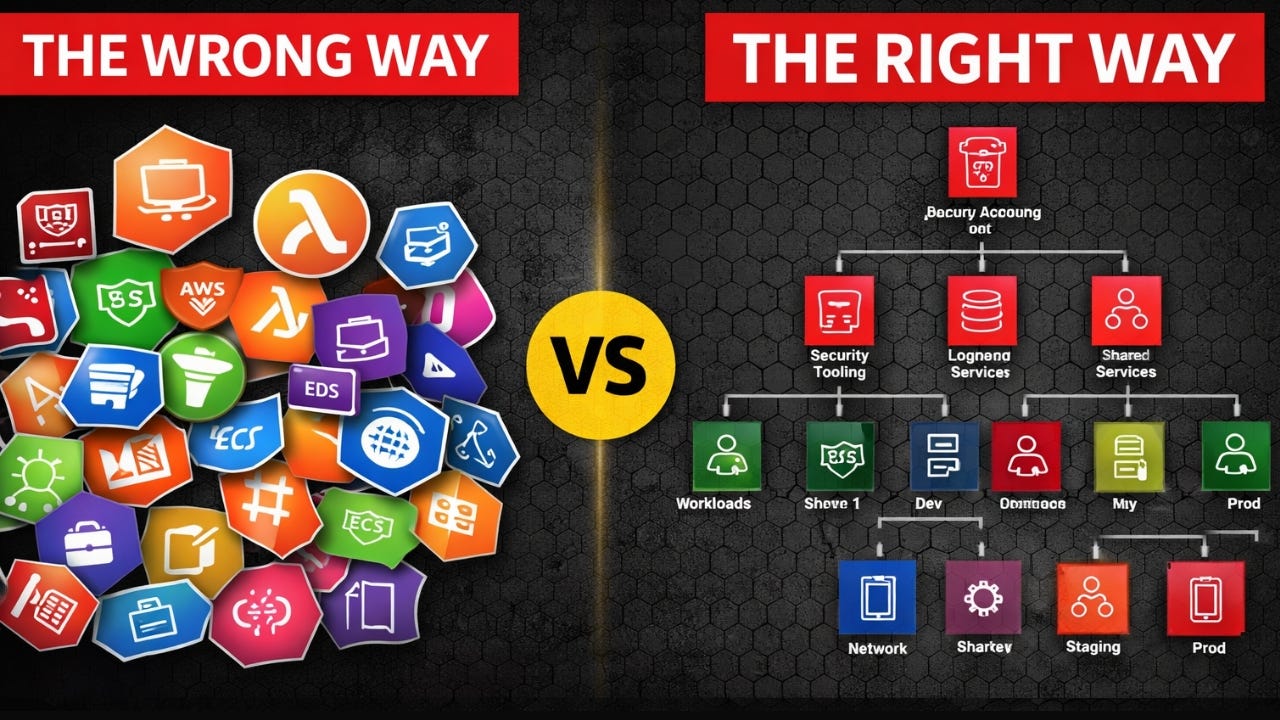
But here’s the uncomfortable truth: most people are still learning AWS security the wrong way.
They approach it like a checklist. They try to understand every AWS service. They jump from GuardDuty tutorials to Config deep dives to Security Hub dashboards. They collect certifications. They memorize console settings. And they assume that more services understood equals more security achieved.
One of the biggest misconceptions in cloud security is this:
“To secure AWS properly, I need to understand every AWS service.”
That’s not just wrong .. it’s strategically misguided.
AWS has over 200 services, and that number continues to grow. You cannot memorize your way into architectural competence. More importantly, security failures rarely happen because someone didn’t understand an obscure feature in a niche service. They happen because the core control layers were weak. IAM was over-permissioned. VPCs were flat. Logging wasn’t centralized. Organizations weren’t structured. SCPs weren’t enforced.
Those are architectural failures, not feature failures.
If you master five foundations, you can reason about almost any AWS environment: IAM, VPC, Logging, AWS Organizations, and SCPs. Everything else builds on top of these layers. If IAM is weak, every service becomes weak. If VPC segmentation is poorly designed, containment fails. If logging is local and mutable, investigations fail. If Organizations are not structured properly, governance becomes inconsistent. If SCPs are not used correctly, blast radius becomes unlimited.
You do not need to understand 200 services. You need to understand the control planes.
The Wrong Way: Service-by-Service Security
Let’s be honest about how most AWS environments are secured.
Teams start with IAM best practices and enable MFA. They turn on GuardDuty and AWS Config. They enable CloudTrail. They switch on encryption. They promise to centralize logging “soon.” They plan to introduce SCPs “once things stabilize.”
On paper, everything looks secure. Security tools are enabled. Dashboards are populated. Alerts are firing.
But when security is implemented service by service, subtle problems begin to emerge. Controls overlap in confusing ways. Responsibilities are unclear between teams. Enforcement gaps appear between identity, network, and logging layers. Logging exists but isn’t designed to support real forensic investigations. Guardrails are technically present but bypassable. Multi-account isolation exists in theory but not in structure.
The result is not a secure system. It is a collection of enabled tools.
Tools do not equal architecture.
Learning AWS security by memorizing service features mirrors this flawed implementation pattern. It produces professionals who can configure individual services but struggle to reason about system-wide risk. And in 2026, that gap matters more than ever.
The Shift: From Services to Architecture
This is where the AWS Security Reference Architecture (AWS SRA) changes your thinking.
The AWS SRA is not a product. It is not a new service. It is a holistic set of guidelines for deploying AWS security services in a multi-account environment. It provides a reference architecture that shows where services should live, how they interact, how they are managed, and how governance should be structured. It reflects years of AWS enterprise customer experience and distills that into architectural patterns.
The SRA forces you to think in layers and boundaries rather than features.
Instead of asking, “What services do we have enabled?” you start asking deeper questions. Do we have a dedicated log archive account? Do we have a separate security tooling account with delegated administration? Are workload accounts isolated properly? Is the management account hardened? Are guardrails enforced through SCPs at the right organizational units? Are findings aggregated centrally? Are logging controls immutable?
You gap against architecture, not against features.
The SRA also changes how you view responsibility. Security is no longer something bolted onto workload accounts after deployment. It is baked into account structure, OU design, and delegated administration models. It enforces defense-in-depth not by stacking tools randomly, but by placing controls deliberately at organizational, identity, network, and workload layers.
That architectural mindset is what separates someone who can configure AWS from someone who can secure it at scale.
A New Era: Vibe Coding and Agentic AI
Now layer in what’s happening in 2026.
Vibe coding is becoming normal. Engineers describe intent, and AI copilots generate infrastructure-as-code. Agentic AI systems are beginning to autonomously call AWS APIs, provision resources, scale systems, and modify configurations based on defined goals.
In the next three to five years, more cloud resources will likely be created by AI systems than by humans. Infrastructure velocity will increase dramatically. The friction between idea and deployment will shrink.
If your security model depends on manual review, you will lose control.
AI systems will not forget to enable encryption. They will not intentionally misconfigure services. But they may create over-permissioned roles to “make things work.” They may deploy into unintended Regions. They may bypass logging patterns if those patterns are not structurally enforced. They will optimize for functionality unless governance is embedded into the architecture.
Weak architecture amplified by AI becomes systemic risk.
Strong architecture amplified by AI becomes leverage.
This is why learning AWS security through service memorization is becoming even less relevant. The future belongs to those who design guardrails that operate regardless of who — or what — is provisioning infrastructure.
How to Prepare for What’s Coming
To prepare for the future of AWS security, shift your focus.
Move toward architectural thinking instead of service memorization. Understand how IAM boundaries interact with SCP ceilings. Learn how multi-account isolation reduces blast radius. Design logging as forensic infrastructure, not just monitoring output. Build governance enforcement mechanisms that do not depend on human vigilance.
Prioritize governance enforcement over manual review. Design for blast radius containment rather than perimeter assumptions. Think about automation-aware security design. Assume that APIs will be called at machine speed and ask whether your guardrails can handle that pace.
The professionals who will thrive in AWS security are not those who can navigate every console tab. They are those who can design systems that hold under pressure, under scale, and under automation.
AWS security is not shrinking. It is maturing. And the learning path must mature with it.
If you want to build real AWS security capability in 2026 .. not just pass exams or configure dashboards .. you need to think like an architect. That is exactly why I built my new course focused on mastering AWS security through real-world failures and architectural design. If you are serious about future-proofing your cloud security career in the age of vibe coding and agentic AI, this is where you start.
Because the future of cloud security belongs to those who understand systems, not just services.
You can check it out below. If you are a paid subscriber you get it for free.
Thanks for supporting this newsletter