If Your Cloud Security Projects Look Like Tutorials, You’re Doing It Wrong.
You Don’t Need More Certifications. You Need Better Cloud Security Projects.
If you want your cloud security profile to stand out in 2026, you need to stop thinking in terms of “labs” and start thinking in terms of real organisations, real constraints, and real risk.
A key mistake I see most cloud security candidates do is do projects for the sake of doing something.
They deploy random services, follow tutorials step by step, and end up with a list of tools they have “used.” That approach no longer works. Everyone can spin up an S3 bucket or click through a console wizard.
What hiring managers are looking for is evidence that you understand why things are built a certain way, what can go wrong, and how security decisions affect engineering teams in the real world.
The strongest cloud security projects emulate real production environments. They tell a story. They show trade-offs. They reflect how security is actually practiced inside organisations.
Below are a few project that consistently differentiate strong candidates from everyone else, not because they are exotic, but because they mirror real-world cloud security work.
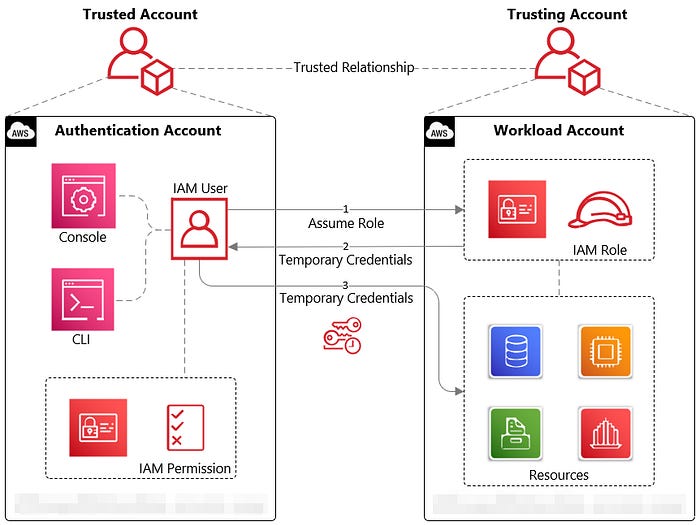
1 — IAM Cross-Account Access: Where Real Cloud Security Starts
Identity and Access Management is not a beginner topic, and that’s exactly why it makes such a powerful project.
In real organisations, everything is multi-account. You have separate accounts for workloads, shared services, logging, and security. Engineers do not log into everything directly. Access is delegated, scoped, and constantly reviewed.
A strong project here is not “create an IAM user and attach a policy.” Instead, design a simple multi-account setup and implement cross-account access properly. One account represents a central security or admin account. Another represents an application workload. You define roles that can be assumed across accounts, use trust policies correctly, and enforce least privilege.
The key is to document your thinking. Why did you choose role assumption instead of long-lived credentials? How would this scale to 20 or 100 accounts? What risks exist if a role is over-privileged? How would you detect misuse?
This immediately signals maturity. Anyone reviewing your work can see that you understand how modern cloud environments are structured and why IAM mistakes are so dangerous.
2 — Building a VPC Using Infrastructure as Code
Infrastructure as Code is not optional anymore. If your cloud security project involves clicking around the console, it already looks outdated.
A strong project involves defining a VPC using Terraform or another IaC tool and treating it as if it were going into production. You design public and private subnets, route tables, internet gateways, and NAT gateways with intent, not guesswork.
More importantly, you explain the security implications of your design. Why are certain resources in private subnets? What traffic is allowed in and out? How do security groups and network ACLs complement each other? Where would inspection or logging live in a real environment?
This is where many people fall down. They build the VPC but never explain the “why.” A standout project includes diagrams, comments in the code, and a short write-up that explains how the design reduces attack surface and supports future growth.
Security teams spend a huge amount of time reviewing architectures like this. Showing that you can think at this level immediately elevates your profile.
3 — CI/CD Pipelines With Security Built In
Modern cloud security lives inside pipelines, not after deployment.
A meaningful project here is to build a simple CI/CD pipeline that deploys your infrastructure or application and then introduce security checks into that pipeline. This could include static analysis, infrastructure policy checks, or simple misconfiguration detection.
The important part is not the tool you use, but the mindset you demonstrate. You are showing that security is something engineers encounter early, automatically, and repeatedly. You are also showing empathy for developers by catching issues before they reach production.
In your explanation, talk about trade-offs. What happens if a security check is too strict? When should a pipeline block a deployment versus warn? How would this change in a regulated environment?
This mirrors real conversations that happen daily between security and engineering teams. Hiring managers recognise this immediately.
4 — Running a Cloud Security Audit With Prowler
One of the most underrated but powerful projects you can do is a cloud security audit.
Using a tool like Prowler, you scan your environment and generate findings across IAM, logging, networking, and data protection. But again, the value is not in running the tool. The value is in how you interpret the results.
A strong project shows that you can distinguish between signal and noise. You explain which findings matter, which ones are contextual, and which ones would be accepted risks in a real organisation. You might prioritise a handful of critical issues and explain how you would remediate them over time.
This demonstrates judgment, not just technical ability. In real jobs, security professionals are constantly asked to prioritise and explain risk, not just list vulnerabilities.
5 — Secure Logging and Centralised Visibility (Not Just “Turn On CloudTrail”)
Many candidates say they “enabled logging.” Very few show that they understand logging as an architectural problem.
A standout project designs centralised logging properly. Multiple accounts send logs to a dedicated log archive account. Access to logs is tightly restricted. Logs are immutable, protected from deletion, and monitored for tampering.
What really elevates this project is explaining why this matters. In real incidents, attackers often try to disable or erase logs first. Your project should show how log integrity is protected, what happens if logging is turned off, and how you would detect that.
This demonstrates that you understand security from an incident response and forensics perspective, not just compliance.
6 — Break-Glass Access and Emergency Controls
This is a project almost no junior or mid-level candidate thinks about, yet it is extremely common in real organisations.
Design a break-glass access model for emergencies. This could involve a highly restricted admin role, strong MFA enforcement, limited session duration, and clear documentation of when and how it can be used.
The value here is not the technical complexity. It’s the governance thinking. You explain scenarios where normal access fails, how to recover safely, and how misuse would be detected and reviewed.
This tells reviewers that you understand operational reality. Systems fail. People make mistakes. Security has to account for both.
7 — Secrets Management and Credential Hygiene
Another strong project focuses on how applications handle secrets.
Instead of hardcoding credentials or using environment variables everywhere, design a setup where secrets are centrally managed, rotated, and accessed with least privilege. Show what happens when a secret leaks and how rotation limits blast radius.
What makes this stand out is explicitly showing what not to do and then fixing it. Demonstrating insecure patterns and then improving them mirrors how real remediation work happens in production.
Security teams spend a huge amount of time cleaning up poor secrets practices. Showing you understand this pain point is powerful.
8 — Threat Modeling a Cloud Architecture You Built
This is an advanced but extremely effective project.
Take one of your existing architectures — the VPC, CI/CD pipeline, or multi-account setup — and perform a basic threat model against it. Identify realistic threats, likely attack paths, and where controls reduce risk.
You don’t need a formal framework to make this valuable. What matters is that you show structured thinking. What could go wrong? How would an attacker move? Where are your weakest points?
Very few candidates demonstrate this mindset, yet this is exactly how senior security engineers think.
Packaging It Like a Professional
All of this work should live in a single, well-structured GitHub repository. Not as a dumping ground for files, but as a narrative.
Your repository should include infrastructure code, pipeline configuration, audit outputs, and a clear README that explains the scenario you are emulating. Think of it as a case study, not a homework assignment.
This is where many people miss a huge opportunity.
Instead of just sending a link to code, record a short Loom video where you walk through your project. Explain your assumptions. Explain your decisions. Explain what you would do differently in a real enterprise.
This is incredibly powerful. You are no longer just a CV on a screen. You are demonstrating how you think, how you communicate, and how you reason about security under realistic constraints. You can send that video to a recruiter, a hiring manager, or a potential client, and it instantly sets context.
Using platforms like GitHub and Loom this way turns your project into a reusable asset, not a one-off exercise.
Why This Approach Works
The cloud security market has matured. Employers are no longer impressed by tool lists or certifications alone. They want evidence that you understand real systems, real risks, and real trade-offs.
Projects like these work because they mirror how cloud security is practiced in the real world. They show that you can think beyond tutorials, that you understand scale and complexity, and that you can communicate your reasoning clearly.
If you do just one or two projects at this depth, they will carry more weight than ten shallow labs. You are not trying to prove that you can follow instructions. You are proving that you can operate as a cloud security professional.
That is what makes a profile stand out.
If you still need help then check out my video below also which has a complete repo where I have documented these projects for your help !