ChatGPT Prompts To Help Your Cybersecurity Career - 004
Become A Threat Modeling Master With This Prompt
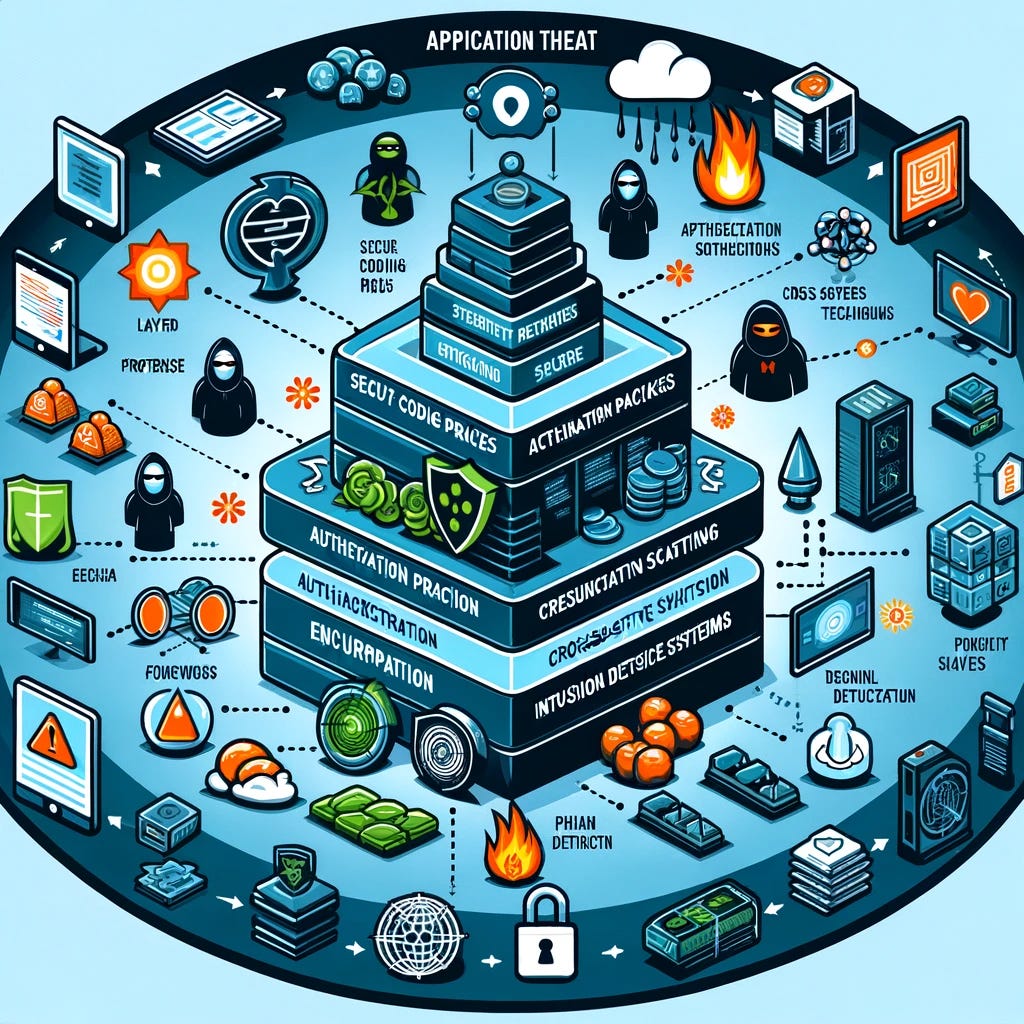
If you are in Cybersecurity then Threat Modeling is a skill you cannot afford to ignore
We are living in a world of application risks and the old excel based risk matrix no longer cuts it
A threat model lets you adopt the view of an attacker to see where an application’s weak points may be present
As defined by OWASP
“A threat model is a structured representation of all the information that affects the security of an application. In essence, it is a view of the application and its environment through the lens of security”
Standard risk management does not dive deep in to applications, how they work and where the potential risks might be whereas Threat Modeling does
The best tool for Threat Modeling honestly is nothing more than a whiteboard and a passion for brainstorming
Free and commercial tools also exist to make the job easier BUT do you know ChatGPT can be a great tool to teach you threat modeling
You can use it to hone your skills by providing it different scenarios and seeing the threat model it generates
The trick is giving it the right prompt and context .. then watch the magic happen
Let’s see how it works !
Let us take a sample application that looks like this
Online Banking Application
Key Components:
Web Application Server: Hosts the online banking application, serving web pages, processing user inputs, and executing business logic.
Database Server: Stores sensitive information such as account details, transaction history, and personal information of the users.
Authentication Server: Manages user authentication and authorization. It handles login requests and token generation for session management.
Firewall: Protects the network by filtering incoming and outgoing traffic based on a set of security rules.
Software:
Web Server Software: Apache HTTP Server, configured to serve the online banking application.
Database Software: MySQL, used for storing all persistent data related to the application.
Authentication Service: OAuth 2.0 based authentication service, used for managing user sessions and protecting access with tokens.
Encryption Software: TLS (Transport Layer Security) for securing data in transit between the client and the server.
Network Configurations:
Demilitarized Zone (DMZ): The web application server is placed in a DMZ, isolating it from the internal network containing the database server.
Firewall Configurations:
Inbound rules: Allow HTTPS traffic to the web application server; deny all other inbound traffic.
Outbound rules: Restrict outbound traffic from the web application server to only the database server and the authentication server on specific ports.
VPN Access: Required for administrative access to the servers from remote locations, ensuring secure communication channels.
Data Flow:
User Login: The user submits their username and password, which are encrypted and sent to the authentication server over TLS.
Authentication and Token Generation: Upon successful authentication, the authentication server issues a token, which is sent back to the user's browser.
Session Establishment: The user's browser sends the token with each request to the web application server, which validates the token with the authentication server.
Data Retrieval and Modification: User requests for data retrieval or modification (e.g., viewing account balance, transferring funds) are processed by the web application server, which interacts with the database server as necessary. All data transfers between the web application server and the database server are encrypted.
Logging and Monitoring: All transactions and authentication attempts are logged. The system is monitored for unusual patterns that could indicate a security threat.
User Interactions:
Users can login/logout, view account balances, transfer funds, pay bills, and update personal information.
For critical actions (e.g., transferring funds), multi-factor authentication is required.
Users receive notifications for successful and failed login attempts, as well as for transactions above a certain threshold.
How do I get ChatGPT to create a threat model for this ??
Keep reading with a 7-day free trial
Subscribe to ☁️ The Cloud Security Guy 🤖 to keep reading this post and get 7 days of free access to the full post archives.